Our Team
Management and Administration

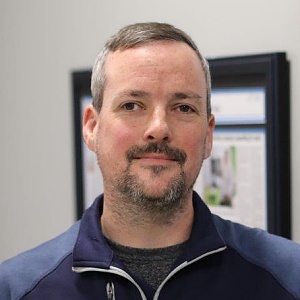
Mark Chestnut
Facilities Manager
Business Development

Gabe McGinnis
Business Development Executive

Karley Lawrence-Losh
Business Development Executive

Nate Arndt
Business Development Executive

Jon Montgomery
Inside Account Manager
Computer Systems

Brianna Nichols
Business System Analyst
Peter Smolinski
Senior Systems Administrator
Ethen Holzapfel
Systems Administrator
Mark Fisher
Computer Technician

Brian Johnson
Computer Technician

Mark Shaffer
Computer Technician

Isaac Baisden
Computer Technician
Ethen Geyer
Computer Technician
Cybersecurity/MSSP

Daniel Fields
MSSP Manager

Ethan Tabata
Junior Security Analyst
Engineering
Mike Taylor
Telecomm Engineer
David Ross
Systems Engineer
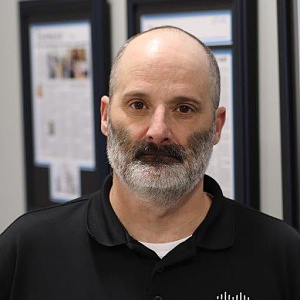
Bruce Barr
Senior Network Engineer

Michael Belcher
Senior Network Engineer

Josh Dingess
Network Engineer
Roger Green
Network Engineer

James Stewart
Sales & Infrastructure Engineer
Software Development
Telecommunications

Michael Stonebreaker
Lead Communications Technician

Bailey Walker
Communications Technician

Raven Stonebreaker
Communications Technician

Eric Sponsler
Communications Technician